JunOS Basics
In this Tutorial We will be discussing about the basic of the JunOS which will include:
- How to setup the root password
- How to change the device name
- How to create a user with admin right using a password and using a SSH key
- How to setup the management interface to ssh in to the switch
- How to create VLAN's
- How to create access and trunk ports
- How to create interfaces range
- How to connect 2 switches
Prerequisites
To complete this tutorial, you will need:
- A laptop running Linux or MacOS. for this tutorial I will be using a laptop running Ubuntu 16
- A console cable. Since all the new laptops today don't come with a USB port, you will need a USB to Console adapter
- The program "Screen"
If you don't have "screen" install it with the command below
sudo apt-get install screen
Accessing the device
- Step 1: Plug the console cable to you device into the console port and start screen as root user on your laptop
screen /dev/ttyUSB0
- step 2: Power on your device
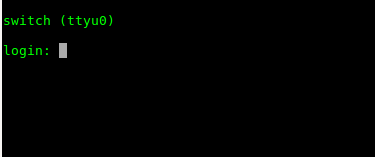
After the device finished booting you will get at the prompt below
- Step 3: Enter the username and password
By default, all Juniper devices username is "root" with no password. At the prompt, just type in root and hit enter
How to setup the root password
When you come from a CISCO world like me, at the beginning it is a little bit confusing when working with JunOS. But, with time running a couple of commands, you get use to the concept.
For us to setup the root password, we need to be in configuration mode (#). Right now our prompt is showing "%". type in
cli
the prompt will change to ">" which is the operational mode and after that type in "edit" or "configuration" to enter the configuration mode
root@switch:RE:0% cli
{master:0}
root@switch> edit
Entering configuration mode
{master:0}[edit]
root@switch#
To setup the root password with a plain-text password the command is "set system root-authentication plain-text-password" Type the command and hit enter. You will be asked to enter a password twice.
root@switch# set system root-authentication plain-text-password
New password:
Retype new password:
{master:0}[edit]
root@switch#
Note: just setting up the password is not enough, you need to save the change that you just made. In JunOS the way to save changes is by typing the command "commit".
But before we save the changes, there is another useful command that allows us to see what are all the changes made to the device before we scan ave the changes and that command is "show | compare"
root@switch# show | compare
[edit system]
+ root-authentication {
+ encrypted-password "$1$vVYnP0uH$YmTKnA.L0W0KGFtTw36NJ/"; ## SECRET-DATA
+ }
The + sign in front of each lines means that those lines will to added to our devices configuration. Note: you can make all you changes and when done you can type the command " show | compare" before you save with "commit" or you can do one change at the time and do "show | compare" and "commit" and go to the next change. I recommend if you are starting to just do one change and "show | compare" then "commit"
Now we can save our first configuration
root@switch# commit
configuration check succeeds
commit complete
{master:0}[edit]
root@switch#
Now that we have the root password set, we are going to give the switch a name: we are going to use "asw-a1-dfw" as name Note: in a production environment I recommend to disable login with root password. We will discuss about this later.
How to change the device name
The command to setup the device name is :set system host-name "device_name"
{master:0}[edit]
root@switch# set system host-name asw-a1-dfw
Do a "show | compare"
root@switch# show | compare [edit system] + host-name asw-a1-dfw;
Then a "commit"
root@switch# commit
configuration check succeeds
commit complete
{master:0}[edit]
root@asw-a1-dfw#
We can see that the device changed name from "switch" to "asw-a1-dfw"
How to create a privileged user
In the session, we are gong to setup 2 users. One user with a password and another user with a SSH key. The user with the password will be called ppaul1 and the user with the SSH key will be called ppaul2.
Setting user with password
Create user ppaul1
root@asw-a1-dfw# set system login user ppaul1 class super-user authentication plain-text-password New password: Retype new password:
root@asw-a1-dfw# show | compare
[edit system]
+ login {
+ user ppaul1 {
+ class super-user;
+ authentication {
+ encrypted-password "$1$LivXhitM$r9CHQgnCiT6nzRt7XhM/k/"; ## SECRET-DATA
+ }
+ }
+ }
root@asw-a1-dfw# commit configuration check succeeds commit complete
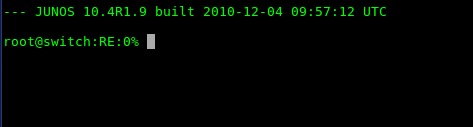
Testing user ppaul1
logout from the user "root" by just typing "exit" until you get to the login prompt
login: ppaul1
Password:
--- JUNOS 10.4R1.9 built 2010-12-04 09:57:12 UTC
{master:0}
ppaul1@asw-a1-dfw>
We can see now that we have login as the user "ppaul1" with a password.in the next step we will create the user ppaul2 with SSH key.
Setting user with SSH key
You can login as root to create the user "ppaul2 or just use the user "ppaul1" to create the user "ppaul2" since ppaul2 is a supe-user
ppaul1@asw-a1-dfw# set system login user ppaul2 class super-user authentication ssh-rsa "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDST4EbXJc9l/AdrVmOZEPl3sxi6qjGIZyPwkupthSdooFHxPxUIh/a5PC9bMk5go6KvRoChpc4L8XuMRsxLTd6Ro6DsWIZieGHFuO/AL9SRUtmevGiSC2q4ibR7ACosJBUvKPRVK8anYnMSL9YWd7lnmVLnW5mvOM3Alhd8aTNKE3/H9ogDt9UfndEJXmieMTLJzGvx65sw6riqa5hh6iOcw02qb3QQCKLSRJmUJQuToY4oo/ZdLl/prEDKQ0I9DSnOxRYIvZxvUsTzwoXVq9X9dWGkKAAMDw7f2DJfa/4uCNT2dKPydApeN0ea2/69VRL3fmTz47y0CC1RTEd8j1j U18pc"
ppaul1@asw-a1-dfw# show | compare
[edit system login]
+ user ppaul2 {
+ class super-user;
+ authentication {
+ ssh-rsa "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDST4EbXJc9l/AdrVmOZEPl3sxi6qjGIZyPwkupthSdooFHxPxUIh/a5PC9bMk5go6KvRoChpc4L8XuMRsxLTd6Ro6DsWIZieGHFuO /AL9SRUtmevGiSC2q4ibR7ACosJBUvKPRVK8anYnMSL9YWd7lnmVLnW5mvOM3Alhd8aTNKE3/H9ogDt9UfndEJXmieMTLJzGvx65sw6riqa5hh6iOcw02qb3QQCKLSRJmUJQuToY4oo/ZdLl/prEDKQ0I9DSnOxRYIvZxvUsTzwoXVq9X9dWGkKAAMDw7f2DJfa/4uCNT2dKPydApeN0ea2/69VRL3fmTz47y0CC1RTEd8j1j U18pc"; ## SECRET-DATA
+ }
+ }
ppaul1@asw-a1-dfw# commit configuration check succeeds commit complete
we can not test yet the user ppaul2 until we setup the management interface and ssh on the device which we are going to do in the next session (see 6.3)
How to setup management interface and SSH
Setting up mamagement interface
The management interface on Juniper switch is called "me0" Also all interfaces are enable by default on Juniper switches. Let use the command "show interfaces me0" to see its output.
Note you need to be in the operational mode (>) to execute this command
ppaul1@asw-a1-dfw> show interfaces me0
Physical interface: me0, Enabled, Physical link is Down
Interface index: 1, SNMP ifIndex: 33
Type: Ethernet, Link-level type: Ethernet, MTU: 1514
Device flags : Present Running No-Carrier
Interface flags: Hardware-Down SNMP-Traps
Current address: 5c:5e:ab:75:6c:81, Hardware address: 5c:5e:ab:75:6c:ff
Last flapped : 2016-07-25 01:49:33 UTC (00:00:06 ago)
Input packets : 1248
Output packets: 280
Logical interface me0.0 (Index 6) (SNMP ifIndex 34)
Flags: Device-Down SNMP-Traps Encapsulation: ENET2
Input packets : 1248
Output packets: 280
Protocol eth-switch
Flags: Is-Primary
We can see that interface is enable and down. Down means there is no cable plugged to it. Now in enter configuration mode and type " show interface me0"
{master:0}[edit]
ppaul1@asw-a1-dfw# show interfaces me0
{master:0}[edit]
ppaul1@asw-a1-dfw# set interfaces
We see that we have no output, this means that true the interface is enable but it is not configured
Let us configure the interface by typing the command " set interfaces me0 unit 0 family inet address 10.192.0.100/24.(Please change this IP address to match your environment)
ppaul1@asw-a1-dfw# set interfaces me0 unite 0 family inet address 10.192.0.101/24
See what will be the changes
{master:0}[edit]
ppaul1@asw-a1-dfw# show | compare
[edit interfaces]
+ me0 {
+ unit 0 {
+ family inet {
+ address 10.192.0.101/24;
+ }
+ }
+ }
Now save the changes
ppaul1@asw-a1-dfw# commit configuration check succeeds commit complete
check again the interface
ppaul1@asw-a1-dfw# show interfaces me0
unit 0 {
family inet {
address 10.192.0.101/24;
}
}
we see that now we have an ip address set for on the interface
Next step it to plug a cable to the interface and check the link on the interface to see if the link is "up". get back in operational mode and type "show interfaces me0" or form the configuration mode you can just type "run show interfaces me0"
ppaul1@asw-a1-dfw# run show interfaces me0
Physical interface: me0, Enabled, Physical link is Up
Interface index: 1, SNMP ifIndex: 33
Type: Ethernet, Link-level type: Ethernet, MTU: 1514, Speed: 1000mbps
Device flags : Present Running
Interface flags: SNMP-Traps
Link type : Full-Duplex
Current address: 5c:5e:ab:75:6c:ff, Hardware address: 5c:5e:ab:75:6c:ff
Last flapped : 2016-07-25 02:05:21 UTC (00:00:44 ago)
Input packets : 1248
Output packets: 283
Logical interface me0.0 (Index 7) (SNMP ifIndex 34)
Flags: SNMP-Traps Encapsulation: ENET2
Bandwidth: 0
Input packets : 0
Output packets: 3
Protocol inet
Flags: Is-Primary
Addresses, Flags: Is-Default Is-Preferred Is-Primary
Destination: 10.192.0/24, Local: 10.192.0.101, Broadcast: 10.192.0.255
We see from the output that the interface is up .The next step will be to setup enable SSH
Enable SSH
We just need one simple command to enable SSH on the device. The command is "set system services ssh"
ppaul1@asw-a1-dfw# set system services ssh
ppaul1@asw-a1-dfw# show | compare
[edit system]
+ services {
+ ssh;
+ }
{master:0}[edit]
ppaul1@asw-a1-dfw# commit
configuration check succeedscommit complete
Now let us test user "ppaul2" . on your laptop open a terminal window and type in "ssh ppaul2@10.192.0.101" (Change IP address with your IP address you setup)
Testing user ppaul2
ssh ppaul2@10.192.0.101
--- JUNOS 10.4R1.9 built 2010-12-04 09:57:12 UTC
{master:0}
ppaul2@asw-a1-dfw>
We are able to login to the device with user "ppaul2: without a password. In the next session we are going to create 4 VLANs.
How to create VLANs
In this session we are going to create 4 VLAN's
- Vlan private1-a-dfw with ID 2000
- Vlan private1-b-dfw with ID 2001
- Vlan private1-c-dfw with ID 2002
- Vlan private1-d-dfw with ID 2003
The command to create the VLAN's is " set vlans vlan_name vlan-id XXXX"
ppaul2@asw-a1-dfw# set vlans private1-a-dfw vlan-id 2000
Check the output before saving
ppaul2@asw-a1-dfw# show | compare
[edit]
+ vlans {
+ private1-a-dfw {
+ vlan-id 2000;
+ }
+ }
ppaul2@asw-a1-dfw# commit configuration check succeedscommit complete
We have the first VLAN, we are going to use the same command the create the other VLAN's by changing the vlan_name and the the vlan_id. After create all the VLAN's type the command "show vlans"
Output
ppaul2@asw-a1-dfw# show vlans
private1-a-dfw {
vlan-id 2000;
}
private1-b-dfw {
vlan-id 2001;
}
private1-c-dfw {
vlan-id 2002;
}
private1-d-dfw {
vlan-id 2003;
}
Now we have all the VLAN's setup, in the next session we are going to create 5 interfaces-range.
How to create interfaces range
As I mentioned earlier when setting up the management interface me0, all interfaces on the Juniper devices are enable by default. Setting up interfaces range, will help better organized and manage the device. Think of interface range as a group or category in which you can group interfaces with the same configuration set. We mentioned earlier that by default all interfaces on the Juniper devices are enable. For security reason, it is best to disable all interfaces by default and just enable it when it has to be used.
The first interface-range we are going to create is the interface-range called disable and will have ford description DISABLED and we will set the interface to disable.
ppaul2@asw-a1-dfw# set interfaces interface-range disable disable description DISABLED
{master:0}[edit]
ppaul2@asw-a1-dfw# show | compare
[edit interfaces]
+ interface-range disable {
+ description DISABLED;
+ disable;
+ }
we can see that we create an interface-range name disable with a description DISABLE and we disable the interface range.
we can not save the changes we made until we interface range has a member. if we try to save the change right now with the interface-range having a member will we get:
ppaul2@asw-a1-dfw# commit error: interface-range 'disable' has no member/member-range statements error: interface-ranges expansion failed